RDP Protocol, or Remote Desktop Protocol, is a networking method that allows users to easily and remotely connect to their desktop or server. With the help of RDP, you can access systems effortlessly over the internet or a local network and work with them as if you were sitting right in front of the machine. This protocol is extremely popular in professional and corporate environments because it greatly simplifies system management and technical support.
In this article, we will take a closer look at what RDP is, how it works, its costs and usage methods, and the features it offers compared to its competitors. So, stay with us at 1gbits.
What Is RDP? A Simple, Fundamental Definition
Remote Desktop Protocol (RDP) is software developed by Microsoft that enables users to securely access their Windows desktops or servers remotely. By transmitting graphical data and user inputs over a network, this protocol provides an experience very similar to working directly on the system itself.
RDP is mainly used for system administration, technical support, and handling daily tasks in work environments. It offers many features such as data compression, information encryption, and support for multiple simultaneous connections. In addition, RDP allows users to take advantage of their servers’ hardware and software resources without needing to be physically present.
One of the key reasons behind RDP’s exceptional popularity is that instead of transmitting all processing data, it only sends the visual output of the results. This means you can connect to a server with 32 CPU cores and 128 GB of RAM using a low-end laptop or even an Android phone and fully utilize that computing power.
The Concept of RDP in Network Engineering
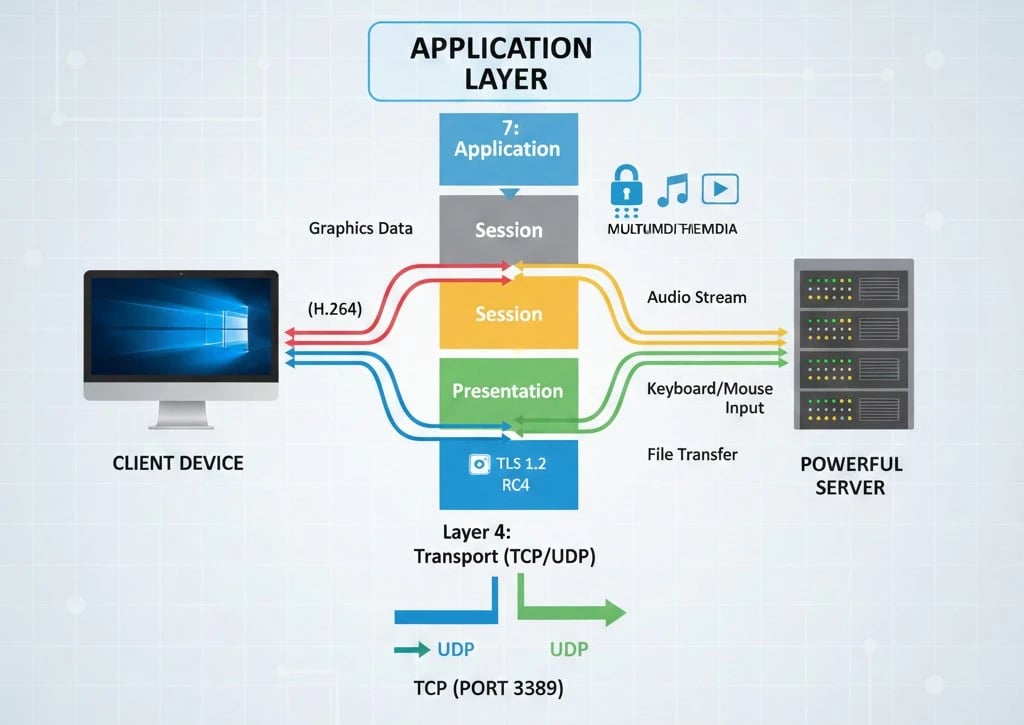
In the OSI model hierarchy, RDP operates at the Application Layer (Layer 7). However, its encapsulation and transmission processes span layers 4 through 7.
|
Feature |
Technical Details |
|
Operating Layer |
Application Layer (OSI Layer 7) |
|
Base Standards |
ITU-T T.120, T.128 |
|
Default Port |
3389 (TCP and UDP) |
|
Transmission Method |
Client–Server |
|
Default Security |
TLS or RC4, depending on the version |
By default, this protocol uses TCP port 3389. In modern versions, starting from Windows 8, UDP is also used to improve multimedia data transfer performance and reduce latency. RDP’s ability to create up to 64,000 separate virtual channels for transmitting different types of data makes it one of the most flexible communication protocols available.
How RDP Works in Data Transfer and Remote Desktop Display?
The Remote Desktop Protocol (RDP) operates based on a client server architecture. This means the user, acting as the client, connects to the server, sends requests, and the server returns the required data after processing them.
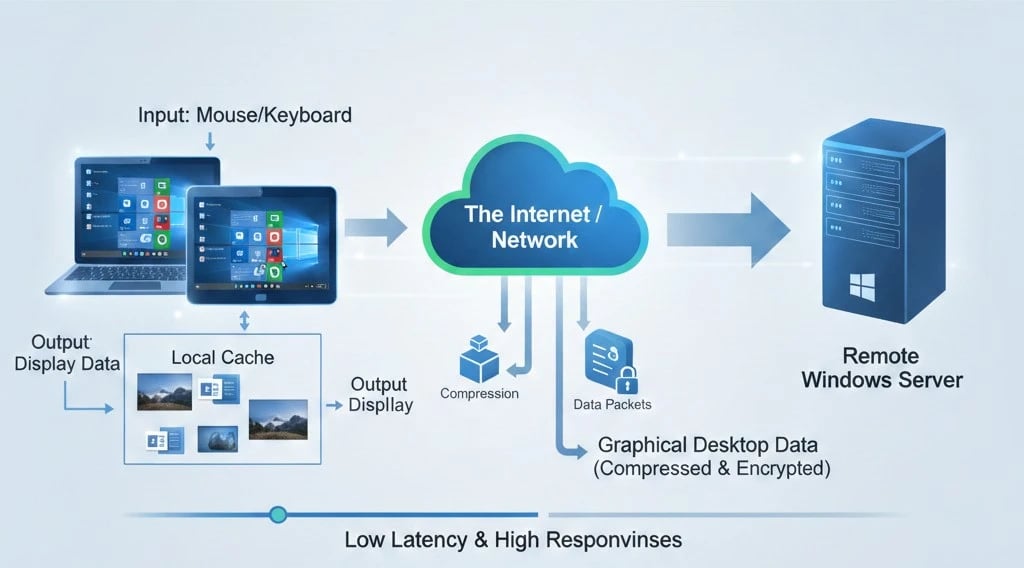
When a user connects to a server using RDP, graphical data is automatically compressed and sent to the client. On the user side, this data is received and reconstructed so that the desktop image can be displayed. The purpose of this process is to create an experience similar to working directly on a personal system. To reduce bandwidth usage, RDP uses techniques such as bitmap caching. This means static images like backgrounds or icons are not resent and are instead loaded from local cache memory.
In addition to visual data, RDP also transfers user inputs such as mouse clicks and keyboard keystrokes to the server. This two-way communication enables smooth interaction with the system. By using compression and encryption, the protocol also maintains connection security and protects sensitive data during transmission.
For more information about RDP clients and how to use them, we recommend reading the article What is an RDP Client?.
Advanced RDP Architecture and Infrastructure Components
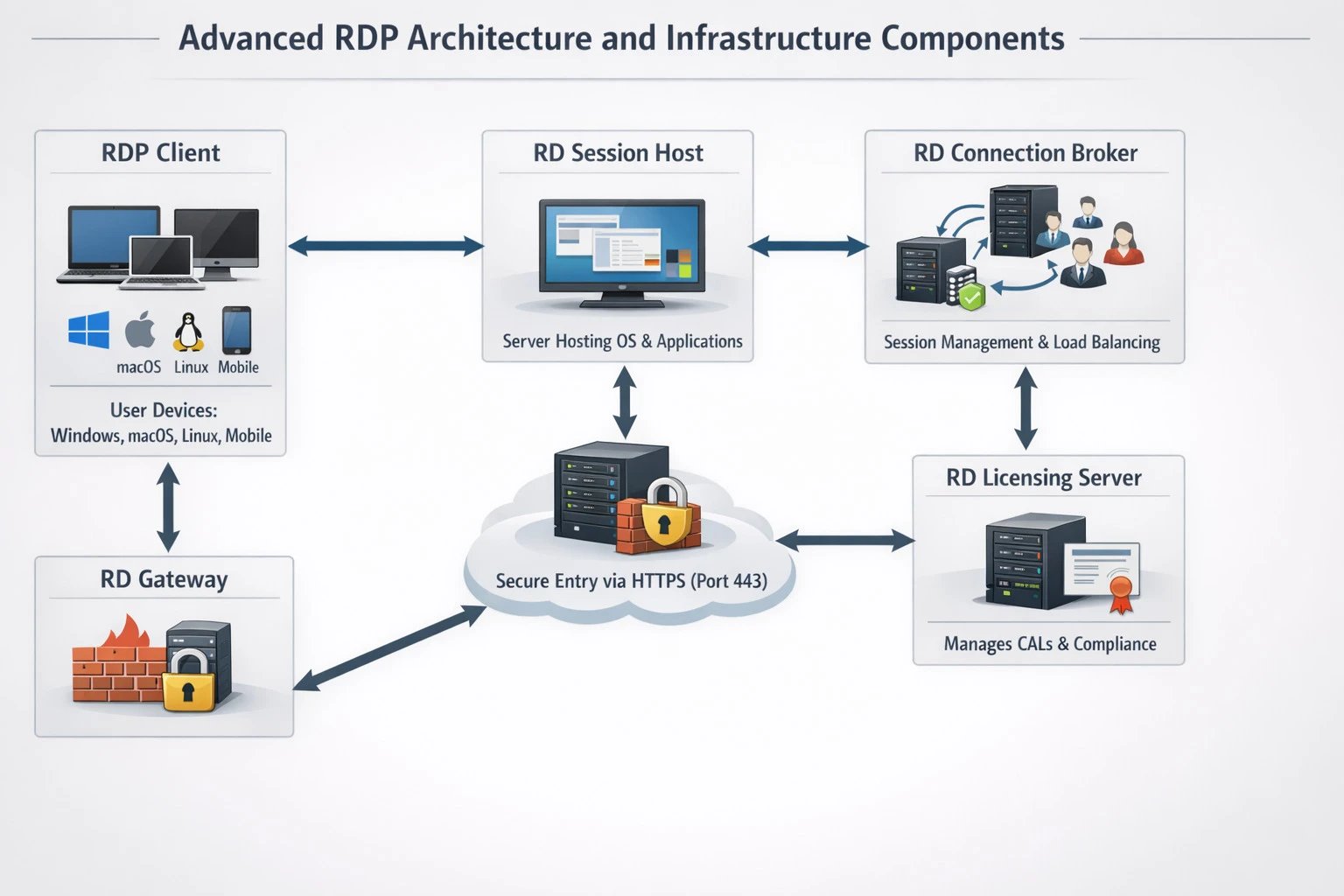
Contrary to the common assumption that RDP is merely a connection between two computers, in large scale and enterprise environments this protocol relies on a multilayer and sophisticated architecture that ensures system stability and scalability.
-
RDP Client: Software that runs on the end user’s device, whether Windows, macOS, Linux, or mobile, and is responsible for displaying the desktop image and sending user inputs.
-
RD Session Host: A server where the operating system and applications are installed and where user sessions are hosted.
-
RD Connection Broker: The central session management component responsible for load balancing across multiple servers and reconnecting users to their existing sessions.
-
RD Gateway: This component acts as a secure entry point and encapsulates RDP traffic within HTTPS on port 443. It allows users outside the organization’s internal network to access resources without requiring a VPN.
-
RD Licensing Server: Responsible for managing user access licenses, known as CALs, and ensuring compliance with Microsoft licensing policies.
In an advanced enterprise scenario, the user first connects to the RD Gateway. After initial authentication, the gateway forwards the request to the RD Connection Broker. The broker determines which Session Host server has the lowest load or whether the user already has an existing active session.
Once the destination is selected, a communication tunnel is established and graphical data and user inputs are exchanged between the client and the target server. Within the internal network, this communication typically uses port 3389, while at the network edge it passes through port 443.
Core Components of the Protocol Stack
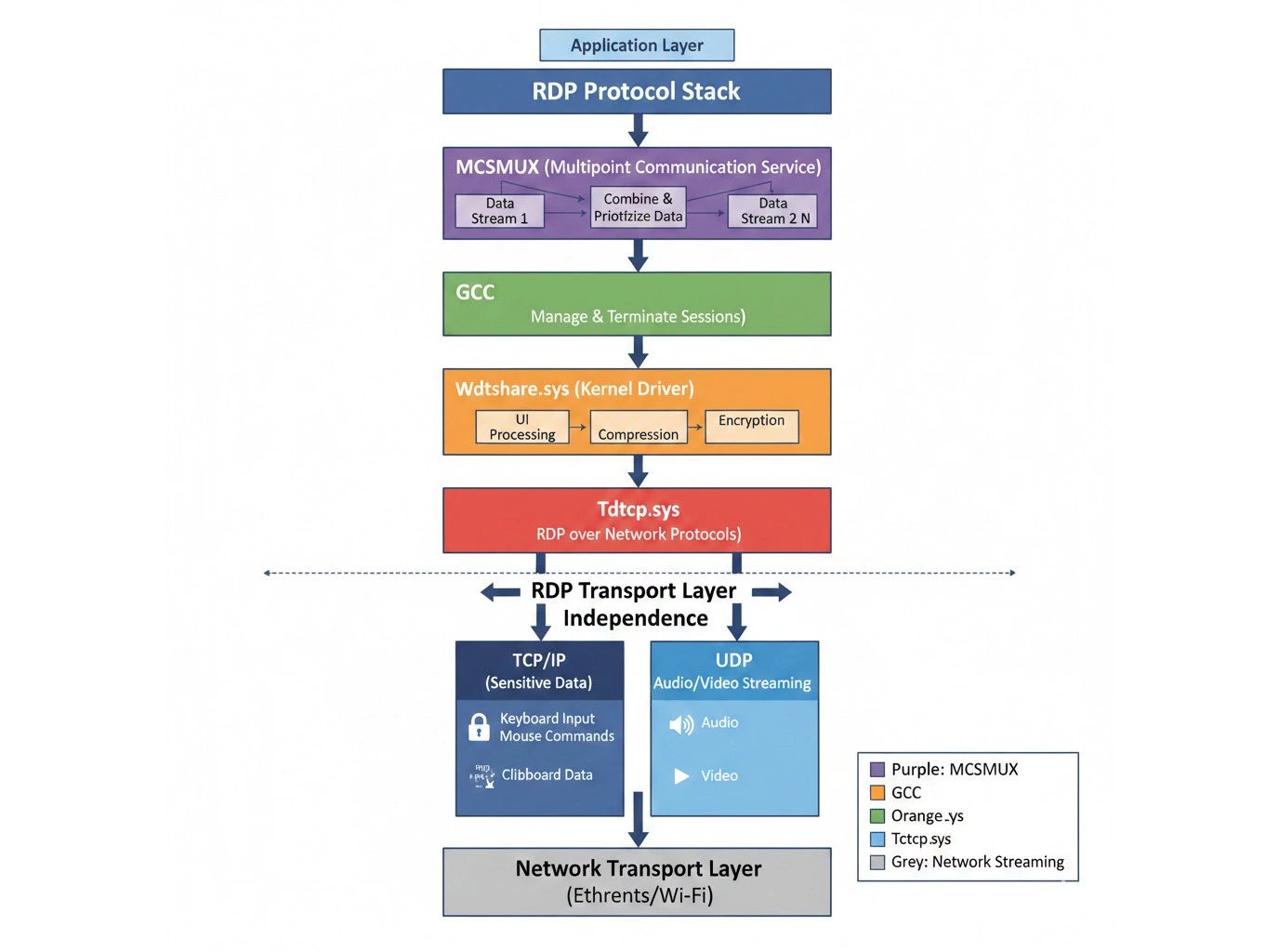
To examine the process in greater depth, it is necessary to look at the RDP protocol stack itself. The RDP stack consists of the following key components, whose coordination ensures a smooth user experience:
-
MCSMUX (Multipoint Communication Service): This component maps different types of data onto defined virtual channels and assigns priorities to them. In practice, MCSMUX combines multiple data streams into a single managed entity.
-
GCC (Generic Conference Control): This layer is responsible for creating, managing, and terminating sessions, as well as controlling the resources provided by MCS.
-
Wdtshare.sys: This kernel mode driver serves as the core engine for user interface handling, data compression, and encryption.
-
Tdtcp.sys: This component is responsible for running the RDP protocol over underlying network protocols such as TCP/IP.
One of the key strengths of RDP architecture is its independence from the transport layer. This means that if network transport protocols change in the future, only the transport driver needs to be replaced, while the RDP core remains unchanged. In addition, modern RDP intelligently uses both TCP and UDP. TCP is used for sensitive data, while UDP enables faster transmission of audio and video content.
|
Architecture Layer |
Technical Name |
Primary Function |
|
Application Layer |
RDP Application |
Delivering the desktop or applications to the end user |
|
Sharing Layer |
T.128 (T.Share) |
Managing window and graphics sharing |
|
Multiplexing Layer |
MCS (T.125) |
Separating data into up to 64,000 virtual channels |
|
Adaptation Layer |
X.224 |
Adapting ISO services to the TCP/IP protocol |
|
Security Layer |
Security Layer |
RC4 or TLS encryption and digital signing |
|
Transport Layer |
TCP / UDP |
Physical packet transmission across the network |
If you want to explore more details about RDP architecture and compare it with RDS and VDI, the articles RDS vs RDP and VDI vs RDP can provide useful insights.
What Are the Real World Use Cases of RDP?
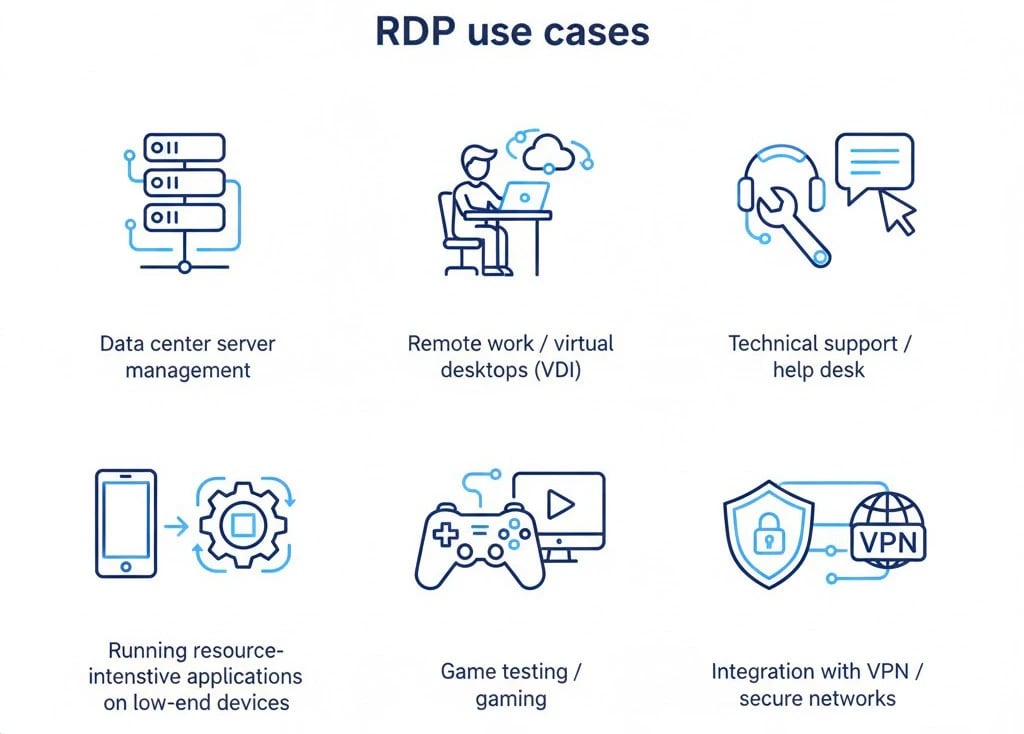
Due to its flexibility and high efficiency, the RDP protocol is used across a wide range of business and technical activities.
-
Data center server management: Network administrators use RDP to manage thousands of servers that may be located in different countries, without the need to physically visit the data center.
-
Remote work: Employees can connect to Cloud PCs or virtual desktops, also known as VDI. This ensures that sensitive company data never leaves secure servers and only the visual output is displayed on the employee’s laptop.
-
Technical support and help desk: IT specialists can access a user’s desktop with permission and resolve software issues directly.
-
Running resource intensive applications on low end devices: Heavy engineering software or video editing tools can be executed on powerful servers and controlled through RDP using a basic tablet or lightweight device.
-
Game testing and gaming: Services such as DeskIn use optimized versions of RDP to test high graphics games that require extremely low latency.
-
Integration with VPN: RDP is often used alongside VPNs or secure tunnels so that, in addition to RDP encryption, the entire connection to the organization’s internal network remains protected.
These examples represent only a portion of RDP use cases. For more information about different RDP applications, you can read the article Uses of Remote Desktop Protocol.
RDP in Different Windows Versions and Licensing Limitations
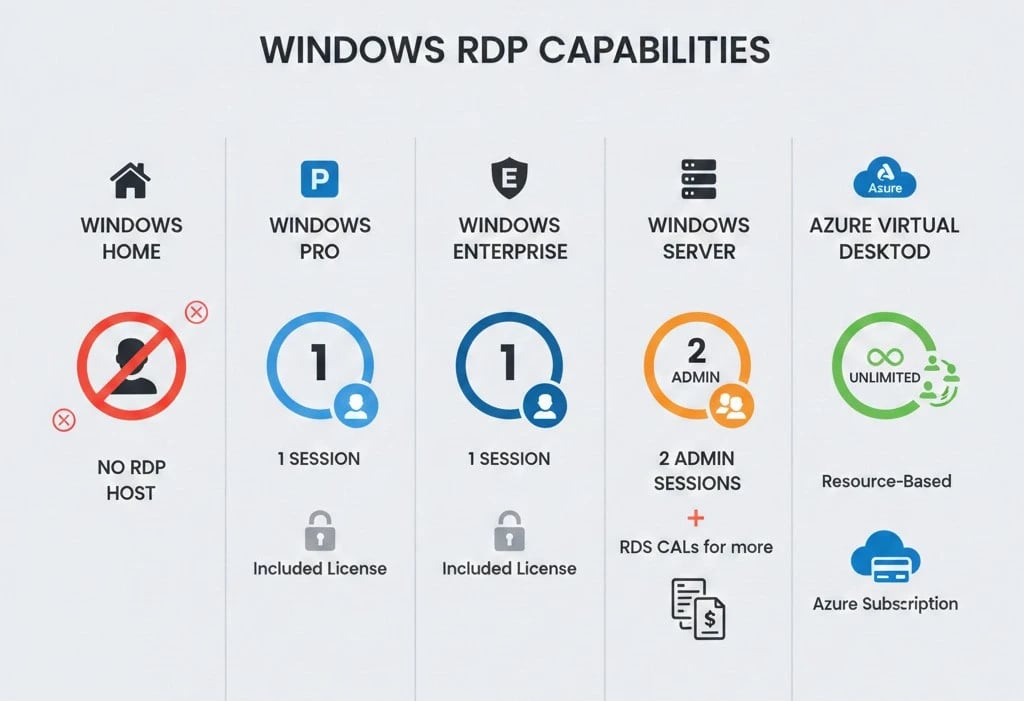
Microsoft restricts RDP capabilities based on the operating system edition and licensing model in order to maintain clear distinctions between Home, Professional, and Server versions.
|
Windows Version |
RDP Host Capability |
Concurrent Sessions |
RDS CAL Required |
|
Windows Home |
No |
0 |
No |
|
Windows Pro |
Yes |
1 |
No |
|
Windows Enterprise |
Yes |
1 |
No |
|
Windows Server |
Yes |
2 (administrative) |
Yes, for more than 2 users |
|
AVD (Azure) |
Yes |
Unlimited, based on resources |
Yes, shared model |
As shown in the table, Windows Home editions do not support RDP hosting. This means you cannot remotely connect to a Windows Home system, although it can still be used as a client to connect to other systems. Windows Pro and Enterprise editions allow one active remote session.
On the other hand, Windows Server is designed to host dozens or even hundreds of concurrent users. To use this capability, the Remote Desktop Services (RDS) role must be enabled. In Windows Server, licensing is handled in two ways:
-
Per User CAL: A license is assigned per user. That user can connect from any number of devices.
-
Per Device CAL: A license is assigned per device. Any number of users can connect to the server from that specific device.
It is important to note that Microsoft provides a 120-day free grace period for testing licenses on Windows Server. After this period ends, valid licenses must be activated on the server to continue using RDP services legally.
What Is the Difference Between an RDP Server and a VPS?
One of the most common misconceptions among non-technical users is treating an RDP server and a Virtual Private Server (VPS) as the same thing. While these two concepts do overlap, they differ fundamentally in terms of control level and resource ownership.
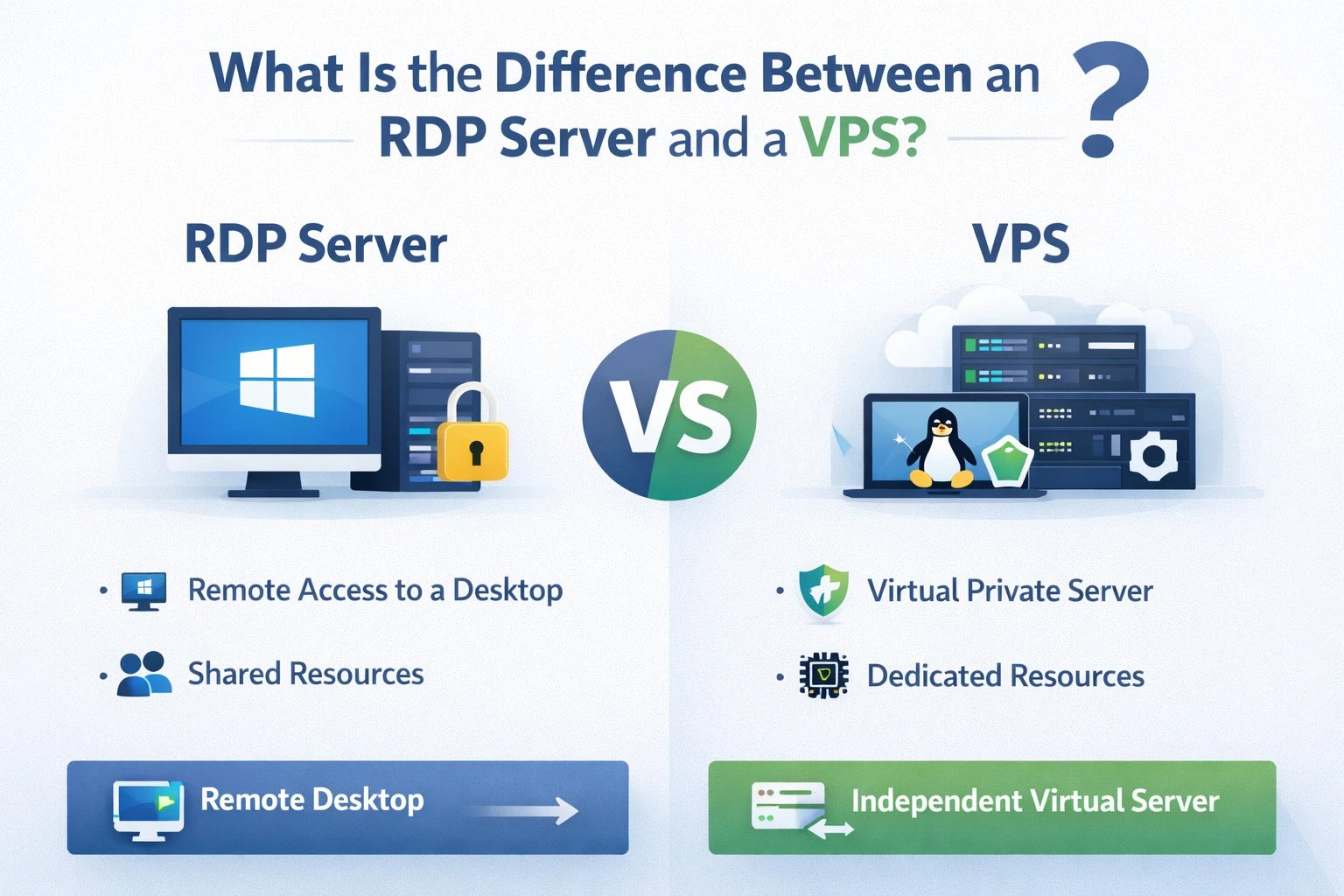
A VPS, or Virtual Private Server, is a portion of a physical server that comes with dedicated resources such as RAM, CPU, and storage, along with full administrator or root level access. In contrast, what is commonly marketed as an RDP server is often a limited user account on a powerful Windows server that is shared among multiple users. In an RDP server environment, you typically do not have permission to install heavy software or modify system level settings. However, with a VPS, you have complete control over the operating system.
With the rise of cloud computing, concepts such as cloud hosted RDP and Windows 365 have emerged. In this model, Microsoft hosts a virtual personal computer in the cloud, and you connect to it using the RDP protocol. This approach combines the simplicity of RDP access with the dedicated performance and control traditionally associated with a VPS.
To further understand how remote access solutions compare, read our guides difference between RDP and VPN and difference between RDP and RDC to learn when each option is most appropriate and how they differ in terms of security and usage.
Network Requirements, Ports, and Protocols
To achieve a high-quality RDP connection, special attention must be paid to the network infrastructure. The standard RDP port is 3389, which operates over both TCP and UDP. However, the port itself is only part of the equation. The most critical factors are latency and bandwidth.
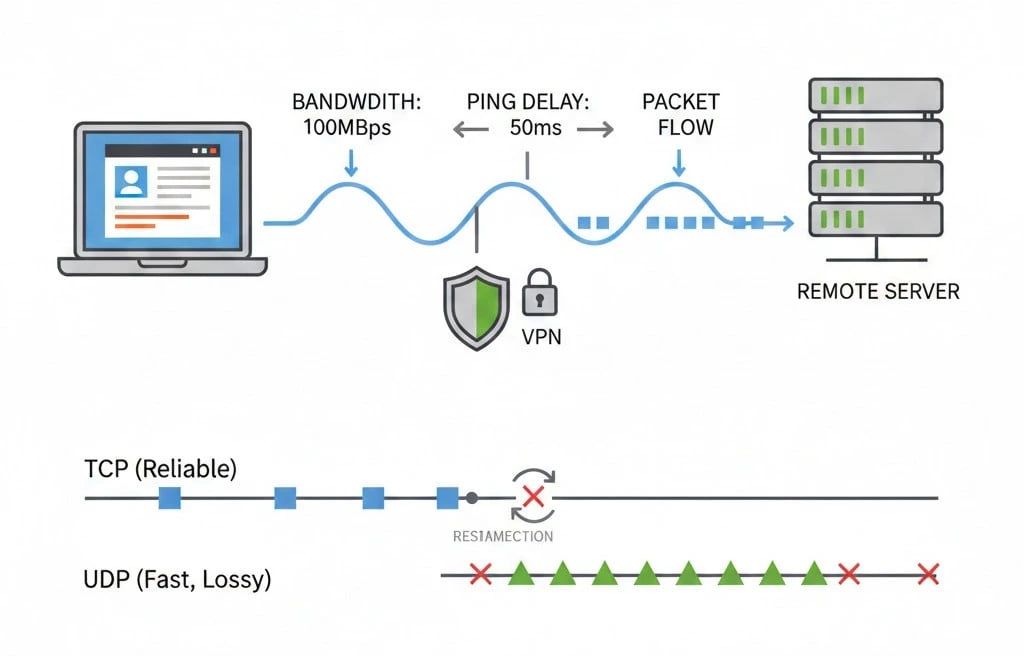
Based on technical analysis, a typical office workload requires between 2 and 5 Mbps of bandwidth. What truly degrades the experience is high latency. If your ping exceeds 100 milliseconds, mouse movements will feel noticeably delayed. In long distance connections or weak internet conditions, enabling UDP can significantly improve performance because this protocol does not halt the entire connection when packet loss occurs and allows faster screen updates.
|
Network Parameter |
Recommended Value for Professional Use |
Impact if Not Met |
|
Ping (Latency) |
Less than 50 ms |
Severe lag in mouse movement and typing |
|
Bandwidth |
At least 5 Mbps |
Blurry image and reduced frame rate |
|
Jitter |
Less than 10 ms |
Sudden screen jumps and audio dropouts |
|
Connection Type |
Wired Ethernet |
Wi Fi instability causes lag |
A few other important points in this section that are worth mentioning:
-
Network traffic: RDP traffic includes screen images, user inputs such as keyboard and mouse activity, and audio. Required bandwidth depends on screen resolution and user activity. RDP generally consumes less bandwidth than full desktop streaming because only screen changes are transmitted.
-
Other protocols: Besides standard RDP over TCP and UDP port 3389, methods like UDP Shortpath are sometimes used in Azure environments to reduce latency. For typical users, properly configuring standard RDP is sufficient.
-
Firewall and remote access: If the server is behind a firewall or directly exposed to the internet, port 3389 must be open, or access provided through a secure tunnel like a VPN or TLS tunnel. Without this, the connection will fail even if the target computer is powered on.
-
Changing the port (optional): For security, administrators sometimes change the default RDP port from 3389 to reduce exposure to automated attacks, though it doesn’t eliminate risk entirely. When changing the port, it must also be configured on the client side and allowed through the firewall.
Below is an explanation of how to configure the port.
How to Change the Default RDP Port?
Changing the default RDP port in Windows is not difficult and can be done using the Registry Editor or Group Policy. To change the port, follow these steps:
-
Log in using an account with administrative privileges.
-
Press Win + R to open the Run dialog, type regedit, and press Enter to open the Registry Editor.
-
Navigate to the following path:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server -
Locate the key fDenyTSConnections and set its value to 0 to enable RDP connections.
-
Create a new key named PortNumber and set its value to the port number you want to use.
-
Restart the system to apply the changes.
An important point to note is that changing the default RDP port can improve security because most cyber-attacks target well known ports such as 3389. For more detailed information about RDP ports and configuration, refer to the article What is RDP Port.
RDP Security Threats
To be honest, RDP is one of the biggest targets for hackers on the internet. Since this protocol provides direct access to the core of the operating system, any weakness can have catastrophic consequences. Some of the most important threats include:
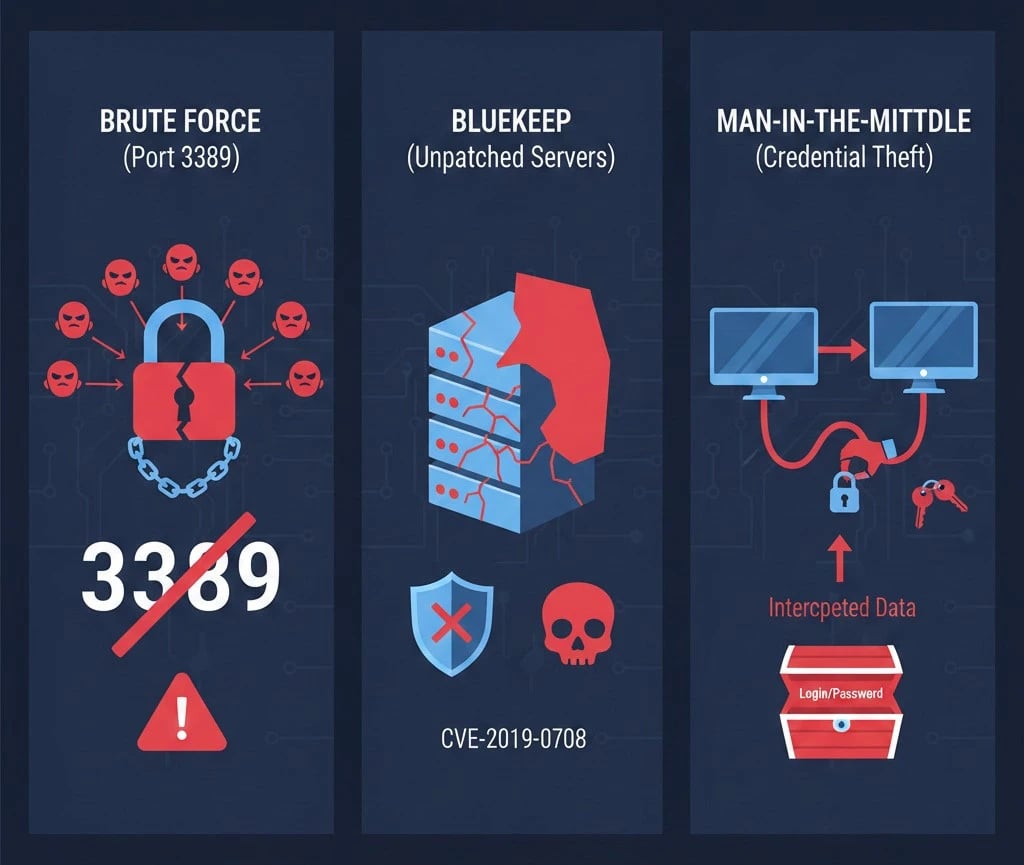
1. Brute Force Attacks
Hackers’ bots continuously scan the internet to find IP addresses with port 3389 open. They then attempt thousands of common passwords in order to gain access. If your password is weak, it is only a matter of time before your system is compromised.
2. BlueKeep Vulnerability
In 2019, the cybersecurity world was shaken by the discovery of the BlueKeep vulnerability. This security flaw allowed hackers to execute malicious code on a server without needing any username or password. The worst part was that this vulnerability was wormable, meaning that an infected system could quickly spread to other systems on the network. Microsoft released security patches, but millions of unpatched systems still exist worldwide.
3. Credential Theft and Man in the Middle (MITM)
If you use older versions of RDP or default settings, a hacker can position themselves between you and the server to intercept data, including your password. Many automated bots simply scan networks to locate RDP servers that use default or weak passwords.
In summary, RDP is not inherently unsafe, but if normal security practices are ignored, it becomes a prime target. Reports indicate that most breaches are caused by these known vulnerabilities. For example, Cloudflare notes that the first major problem is weak passwords and the second is the availability of the RDP port.
How to Secure RDP Properly (Best Practices)
Now that you are aware of the risks, let’s see how to build a strong barrier against hackers. Securing RDP is not a single-step task but a set of layered protections.

-
Enable NLA (Network Level Authentication): This is the first and most important step. NLA requires users to authenticate before a remote session starts. This measure prevents many initial exploits, including BlueKeep.
-
Use strong passwords and MFA: Always use long passwords with at least 16 characters. Even more importantly, implement multi-factor authentication (MFA). Tools such as Duo or Microsoft Authenticator ensure that even if a hacker knows your password, they cannot access the system without the verification code on your phone.
-
Do not expose port 3389 to the internet: This is a golden rule. Instead of opening the port directly, use a VPN. First connect to the VPN, and then access RDP through the internal IP address. Another option is to use an RD Gateway, which transmits traffic over HTTPS.
-
Change the default port (optional but recommended): Although advanced hackers can still find the new port, changing 3389 to a random number, for example 49152, hides the service from thousands of automated bots that only scan for 3389.
-
Enable account lockout policies: Configure the system so that if someone enters an incorrect password, for example 5 times, the account is locked for 30 minutes. This effectively stops brute force attacks.
-
Use a VPN or secure tunnels: The best approach is to place RDP behind a VPN or TLS tunnel. This way, users must first connect to a secure network and then access RDP from within it. This extra layer blocks public access and makes external attacks much more difficult.
Following these steps will help you maintain a secure RDP connection. Remember that when it comes to security, more layers mean better protection.
Comparing RDP with Other Remote Access Technologies
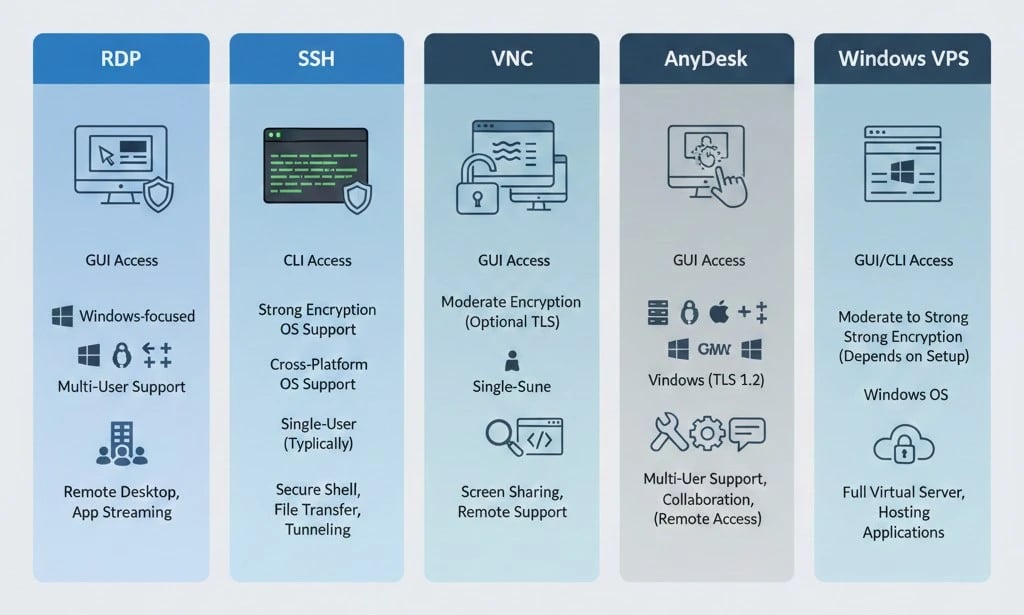
To better understand the differences between RDP and other solutions, consider the table below (features summarized):
|
Feature |
RDP |
SSH |
VNC |
AnyDesk |
VPS (Windows) |
|
Access Type |
Graphical Desktop (GUI) |
Command Line (CLI) |
Graphical Desktop (GUI) |
Graphical Desktop (GUI) |
Full Server/VM (GUI/CLI) |
|
Security (Encryption) |
Encrypted connection (TLS) |
Encrypted (SSH) |
Usually unencrypted or requires add-ons |
Encrypted (TLS) |
Depends on chosen security configuration |
|
Operating Systems |
Windows (Server/Pro), clients on any OS |
Any OS with SSH server (Linux) |
Cross-platform |
Cross-platform |
Any Windows or Linux (depending on VM) |
|
Multi-user |
Native (RDS for multiple users) |
Native (multiple sessions) |
No (single display) |
No (single display) |
Yes (multiple VMs or services) |
|
Mobile Support |
Yes (Windows/Mobile apps) |
Yes (SSH client apps) |
Yes (various VNC apps) |
Yes (Android, iOS) |
If running on a VM |
|
Common Use Case |
Remote server or PC management |
Secure terminal access |
Simple desktop sharing |
Fast remote support |
Full software or web hosting |
As the table shows, each technology has its own strengths and weaknesses. For example, RDP is widely used on Windows and provides a complete graphical user experience, while SSH is primarily used for secure command line access to systems.
Solutions like AnyDesk and TeamViewer use proprietary protocols that are very fast for graphical desktops and offer good security, but they are commercial applications with additional features such as chat and file transfer.
Want a clearer understanding of how RDP and SSH differ in real-world use? Read our guide Difference Between RDP and SSH to explore their key use cases, advantages, and limitations.
RDP Configurations and Clients
RDP client software is available on multiple platforms. Windows includes a built-in client called Remote Desktop Connection (RDC). On Mac or mobile devices, you can use Microsoft Remote Desktop specific to that system, such as the Remote Desktop app on macOS or the mobile version on Android/iOS. On Linux, open-source clients like FreeRDP or Remmina (which support RDP) are commonly used.

Some web services provide RDP through a plugin or applet, but for most standard use cases, installing a client is recommended. Using these clients is straightforward: launch the program, enter the server name or IP address, provide your Windows username and password, and connect to the server.
For more information about alternative clients, see the article What are RDP Client Software.
Cost, Access, and Licensing Models
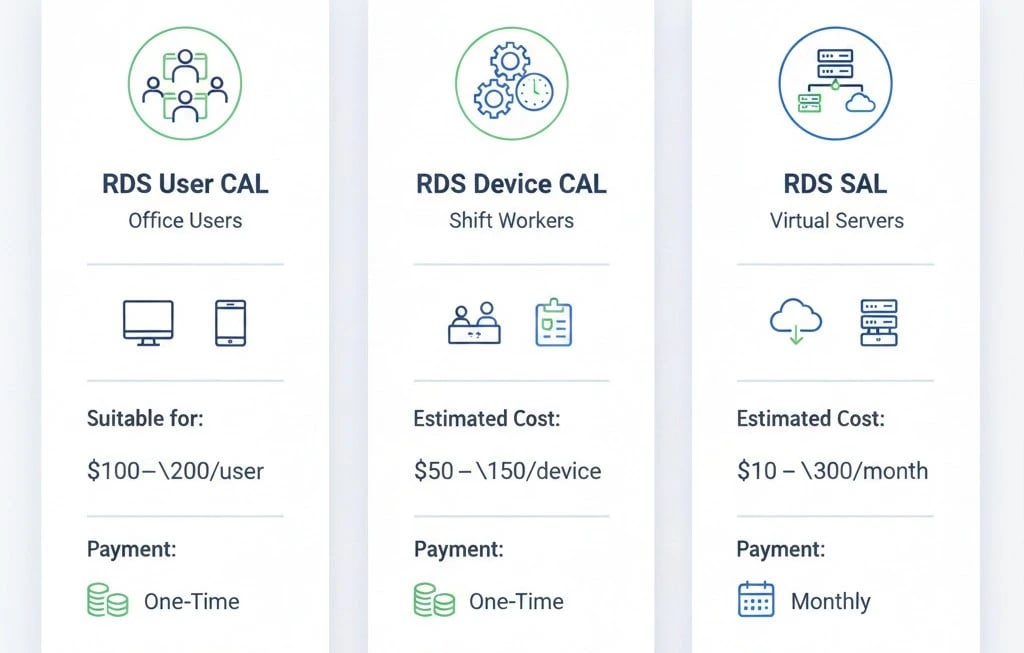
The cost of implementing RDP can range from zero to thousands of dollars, depending on whether it is for personal or organizational use. Remote Desktop functionality is built into Windows Pro and Enterprise editions and is free for a single user. However, in server environments, each user connecting to the server requires an RDS CAL (Client Access License). The difference between CALs and SALs is as follows:
-
RDS CAL (Client Access License): For organizations with on-premise servers. Licenses can be purchased per user or per device.
-
RDS SAL (Subscriber Access License): For cloud service providers under SPLA. Licenses are rented monthly from Microsoft for each user, and the cost is billed to the end customer.
The table below shows approximate costs and licensing models for different workloads:
|
License Model |
Suitable For |
Estimated Cost |
Payment Method |
|
RDS User CAL |
Stable organizations |
~$200 |
One-time payment |
|
RDS Device CAL |
Shift work (Call Center) |
~$150 |
One-time payment |
|
RDS SAL (SPLA) |
Virtual servers (VPS) |
$8–15 |
Monthly |
Keep in mind that if your server is hosted in cloud environments such as AWS or Azure, costs are typically calculated monthly based on usage and may include additional charges for Software Assurance.
Common RDP Issues and Solutions
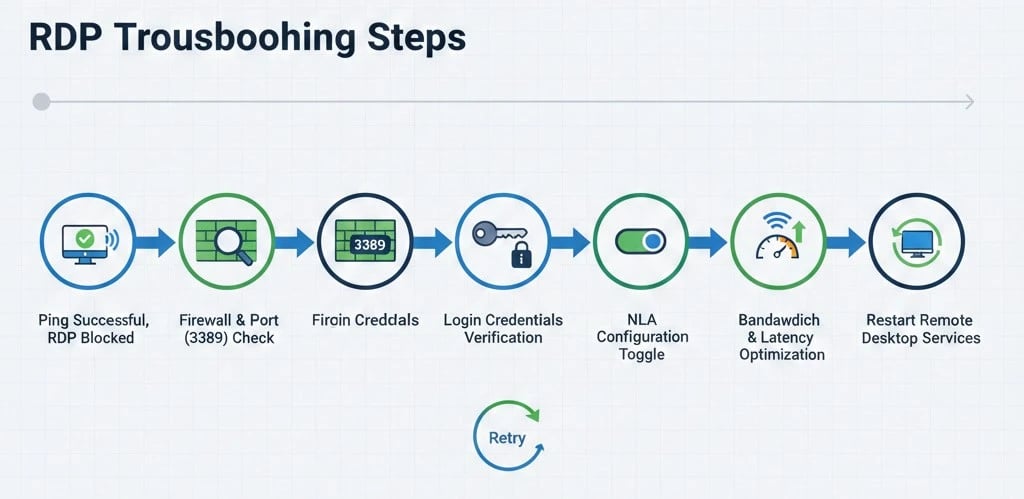
Sometimes RDP connections encounter problems. Here are some examples and their solutions:
Ping works but RDP does not connect
This usually means the network is working, but port 3389 is closed or the Remote Desktop service on the server is not enabled. On Windows Server or Pro editions, check System Properties > Remote to ensure Remote Desktop is allowed and that the Windows firewall is not blocking the port. Sometimes the destination IP is incorrect, or multiple RDP instances are installed and the port has been changed.
Username or password error
Verify that the username and password are correct, especially if you are on a domain. Network Level Authentication (NLA) being enabled or disabled can also cause issues. You can temporarily disable NLA to test if this resolves the problem.
Latency and lag
If the server’s graphics card is weak or bandwidth is low, the display may be slow. Reduce the display quality in the RDP client, for example by lowering color depth, and use a high-speed network. Disabling animations and adjusting graphics settings on both client and server can also improve performance.
Network Level Authentication (NLA) error
If you see the message “This computer can’t connect to the remote computer,” it is likely due to NLA. You can go to Control Panel and disable Allow connections only from computers running Remote Desktop with Network Level Authentication (recommended) and try again.
Bandwidth limitations
If you are used to VNC or AnyDesk, RDP is optimized, but connection quality can still be affected by network conditions. Options like Experience or Performance in the RDP client allow you to select the quality of the connection.
RDP service not running or ping fails
Sometimes the Remote Desktop Services (TermService) needs to be manually restarted. Check this service using services.msc. If ping does not respond, make sure the server is powered on and the IP address has not changed. If the server is behind a router, verify Port Forwarding or VPN settings.
If none of these solutions work, further documentation review or assistance from IT colleagues may be necessary. In most cases, these issues are resolved by correctly configuring ports, firewalls, and Remote Desktop permissions.
Get Secure RDP Now!
As you’ve seen, the Remote Desktop Protocol (RDP) is an incredibly powerful tool for remotely controlling systems and servers. However, with great power comes great responsibility, so security should always be a top priority. If you’re looking for a fast, secure, and reliable experience, our team at 1GBITS is ready to provide the best RDP services. By purchasing the Buy RDP service from 1GBITS, you can enjoy instant setup, full administrative access, servers in over 15 global locations, powerful hardware, and crypto-friendly payments, ensuring a seamless remote desktop experience. We’re here so you can focus on your work without worrying about access or security.
People also read:



![What Is Cold Data Storage? ❄️ [2026 Guide] What Is Cold Data Storage? ❄️ [2026 Guide]](https://1gbits.com/cdn-cgi/image//https://s3.1gbits.com/blog/2026/02/what-is-cold-data-storage-750xAuto.webp)