CloudLinux is a hosting-oriented Linux distribution based on CentOS. It is a commercially supported Linux operating system that can be interchangeable with CentOS. Released in 2010, CloudLinux is essential for any web host prioritizing stability, security, and flexibility. Web hosting providers often favor CloudLinux for delivering uninterrupted, excellent performance to their customers. So, what exactly is CloudLinux OS and why is it so vital for modern Linux VPS environments?
What is CloudLinux OS?

CloudLinux is a prominent Linux distribution among hosting providers. As mentioned, it is based on CentOS but utilizes a modified kernel derived from the OpenVZ kernel. A key component of CloudLinux is its kernel-level technology called LVE (Lightweight Virtual Environment), which enables precise control over CPU and memory resources on a per-tenant basis. This application-level virtualization delivers advanced resource management, enhanced security, and performance optimizations specifically designed for multi-tenant hosting environments.
By handling multitenancy effectively, CloudLinux significantly improves server stability, density, and security. It achieves this by isolating each tenant and providing them with dedicated server resources. This approach allows for an environment similar to a virtual server, unlike traditional shared hosting platforms. This isolation leads to reduced operating costs and lower churn rates, ultimately resulting in better service and increased profitability. With LVE, CloudLinux partitions, allocates, and limits server resources (RAM, CPU, memory) for each tenant, ensuring that individual tenants do not jeopardize server stability. Furthermore, CloudLinux "cages" each tenant to prevent malicious breaches; if one tenant is infected with malware, it remains contained within its isolated environment and does not affect other users on the server.
For those seeking optimal performance and security in their cloud hosting, exploring the options outlined in our guide on the best Cloud VPS can provide valuable insights. Additionally, for users who prefer alternatives to CentOS, understanding what is AlmaLinux can be beneficial, as it is also a popular choice for enterprise environments.
If you're interested in setting up CloudLinux, a great starting point is to learn how to install CloudLinux OS on your server. This will guide you through the initial steps to leverage its powerful features for a stable and secure hosting environment.
Key Tools Used in CloudLinux
CloudLinux empowers administrators to maximize the efficiency and security of their hosting environments. The following tools are integral to CloudLinux's functionality:
LVE Manager
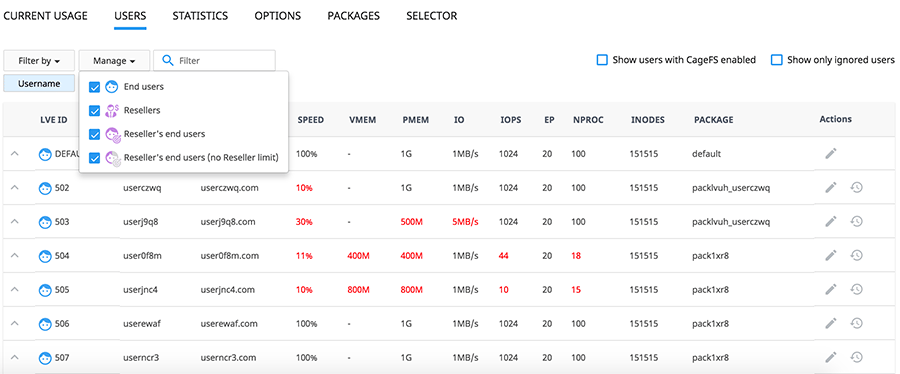
The LVE Manager is a crucial tool that allows administrators to limit server resource usage for each cPanel account. This prevents any single cPanel account (or tenant) from monopolizing all available resources, a common issue in shared hosting environments with multiple tenants. By setting these limits, the LVE Manager ensures fair resource distribution and overall server stability. This tool is often paired with a cPanel VPS to provide a robust control interface for end-users.
CageFS
CageFS creates a virtualized user environment that effectively isolates users, preventing them from seeing other users on the same server. Each user operates within their respective "cages," with full functionality to their necessary system files and tools. The key benefits of CageFS include:
- Only safe binaries are available to the user.
- Users cannot see other users on the server, enhancing privacy.
- Server configuration files are hidden from the user, improving security.
- Users have a limited view of the /proc file system and cannot see other users' processes.
- Any executable malware opened by one user remains contained within their "cage" and does not spread to others.
⚙️ PHP Selector
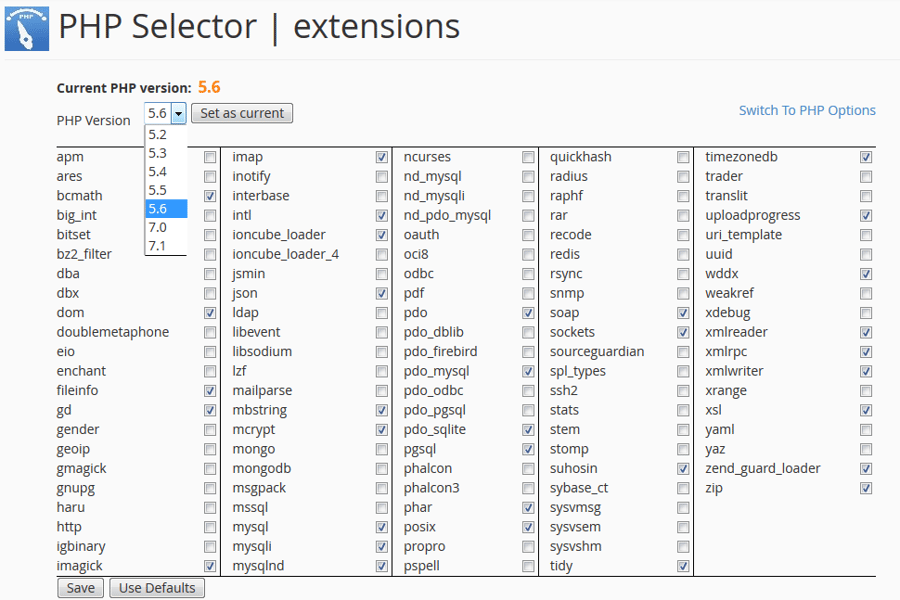
PHP Selector is a valuable tool within CloudLinux that allows users to easily change PHP settings and set limitations within their individual accounts. This is particularly beneficial for users running multiple CMS-style websites on the same server, each potentially requiring different PHP modules or versions. PHP Selector empowers users to choose their preferred PHP versions, ranging from PHP 5.2 to current stable releases, offering flexibility and compatibility for various web applications.
☁️ CloudLinux vs. CentOS: A Comparison
Both CentOS and CloudLinux are Linux distributions, but CloudLinux is frequently used as a direct replacement for the CentOS operating system. While CentOS remains an extremely reliable choice for web hosting solutions, CloudLinux's specialized features streamline administrative tasks, particularly in shared hosting environments.
As discussed, CloudLinux distinctly separates customers into individual tenants on a shared server. This crucial feature safeguards the server from performance degradation caused by the activities of other customers. While both systems share many core features, CloudLinux distinguishes itself with the following advantages:
| Feature | CloudLinux Advantage | CentOS Comparison |
| Stability | Greater stability through isolated environments. | Reliable, but shared resources can impact stability. |
| Efficiency | Increased efficiency in resource allocation. | Standard resource management. |
| Security | Advanced security with CageFS and HardenedPHP. | Standard Linux security measures. |
| Compatibility | Greater compatibility with major control panels. | Good compatibility, but less focused on hosting-specific integrations. |
| Operating Costs | Lower operating costs due to simplified management. | Costs can be higher due to more intensive management in shared hosting. |
⚡ CloudLinux Features
Here is a comprehensive list of the major CloudLinux features:
1. A VPS-like Environment for Your Clients
Through the utilization of LVE, CloudLinux provides a unique set of server resources to each tenant on the server. This means that every website hosted on the server has dedicated resources that are not shared with other accounts. CloudLinux allows for precise monitoring and control of limits such as CPU, RAM, and I/O usage. It effectively isolates users from each other, preventing "noisy neighbor" effects and ensuring that users cannot access configuration files or other private information belonging to others. For a deeper understanding of your server's capabilities, you can also learn how to check hardware information in Linux, ensuring optimal performance and resource allocation.
2. Greater Stability
Thanks to its lightweight and isolated structure, CloudLinux delivers superior user stability. This design prevents individual users from overloading the server. The combination of enhanced stability and separate virtual environments significantly decreases the risk of server downtime, ensuring websites remain online and accessible 24/7. This focused approach to resource management is a key differentiator, making CloudLinux a reliable choice for shared hosting. When deploying such environments, using a high-quality Linux dedicated server provides the necessary raw power to handle these virtualized partitions efficiently.
3. Secured and Hardened Kernel
CloudLinux's increased security measures are designed to prevent malicious users from attacking other website accounts hosted on the same server. This is primarily achieved through the isolated environments provided to each user by LVE. CloudLinux also incorporates HardenedPHP, which proactively addresses security vulnerabilities in older and outdated versions of the PHP programming language. The hardened Kernel further protects against trace exploits and symlink attacks while limiting the filesystem's visibility only to the files users need to access. By using a very secure password for your systems, the security will gain another robust layer.
4. Compatible with All Major Control Panels
CloudLinux boasts extensive compatibility with nearly all major control panels, including cPanel, DirectAdmin, and Plesk. Depending on your chosen hosting plan, you may have the option to directly control your website resources from cPanel, a feature not always available with other operating systems. This high level of compatibility between interfaces offers users the flexibility to choose their preferred control panel, making management seamless. For instance, many providers offer a Plesk VPS server pre-configured with CloudLinux for enhanced control.
5. Monitors and Operates MySQL Usage
Maintaining MySQL stability in a shared hosting environment can be challenging, as individual customer queries can easily slow down an entire site. CloudLinux's MySQL Governor Tool is designed to assist system administrators in identifying and throttling abusive MySQL users in real-time. It meticulously tracks CPU and disk I/O usage for every website account, helping to reduce problematic MySQL queries. With comprehensive support for both MySQL and MariaDB, this tool is an essential asset for any shared hosting provider aiming for optimal performance and fairness. To get started with databases, you can learn how to install MySQL on CentOS 7 effectively.
6. Lower Operating Costs
The CloudLinux operating system simplifies resource allocation for hosting providers, allowing them to efficiently add more tenants to the server without compromising performance. The intuitive administrator interface also provides a more comfortable and less time-consuming platform for management. This efficiency translates directly into fewer hours spent on configuring and monitoring servers, ultimately helping to decrease the overall costs associated with hosting plans. For those looking to maximize their resource allocation and cost efficiency, exploring cloud server solutions can provide a flexible and scalable option that enhances overall performance.
For more insights into cloud infrastructure, understanding what is VPC (Virtual Private Cloud) can further clarify how dedicated, isolated network environments contribute to secure and efficient cloud deployments, complementing the benefits of CloudLinux in a multi-tenant setting.
When considering different hosting solutions, it's also helpful to understand the distinctions between VPS vs. Cloud hosting. While CloudLinux optimizes shared and multi-tenant environments, grasping the broader differences between these hosting types can help you make informed decisions for your specific needs, whether you're looking for dedicated resources of a VPS or the scalability of cloud infrastructure.
✨ Expert Tips for CloudLinux Optimization
- Regularly Monitor LVE Stats: Use the command line tools or the LVE Manager UI to identify which users are consistently hitting their limits. This helps in upselling them to a Cloud VPS.
- Implement MySQL Governor Early: Don't wait for a database crash to enable throttling. Set reasonable limits from the start to ensure overall server responsiveness.
- Utilize HardenedPHP: If you have clients running legacy applications, ensure HardenedPHP is active to patch vulnerabilities in older PHP versions that are no longer supported by the official PHP community.
Conclusion
The final verdict is clear: there are numerous advantages and benefits to using CloudLinux for your hosting needs. It is specifically designed to provide hosting administrators with a smoother and more efficient experience when delivering their services. Its unique features like LVE, CageFS, and MySQL Governor address common challenges in shared hosting environments, leading to improved stability, enhanced security, and optimized resource management.
If you are a hosting provider looking to invest in a dedicated server, we provide the best in the market. Additionally, when looking for Linux VPS hosting, it's important to balance cost with performance, reliability, and security. Our Cloud VPS solutions offer scalable and flexible hosting options tailored to your needs. You can get your dedicated server powered by CloudLinux and make the necessary configurations to start your own shared hosting platform easily. For high-performance needs, consider a high-end dedicated server to ensure maximum resource availability.
For a deeper dive into optimizing your server choices, consider exploring our dedicated Linux server options, which provide enhanced performance and security features to meet your hosting requirements.
People also read:

Leave A Comment