When we want to hack a system, we need a specific exploit to take advantage of a certain operating system, service, or application vulnerabilities. There are many exploits available in the world, ranging from simple scripts to complex multi-stage payloads. Remember that no specific exploit will allow you to exploit all systems; penetration testing is a precise art that requires matching the right tool to the specific environment. You need to find an exploit that will suit your target system. In such cases, the Exploit Database (Exploit-DB) will help us. This article will guide you on installing SearchSploit in Kali Linux and performing your security auditing tasks efficiently.
Exploit-DB is a project of Offensive Security, the same prestigious organization that developed the BackTrack distribution and contributes significantly to the Linux kernel security research. This project is the ultimate archive of exploits, shellcodes, and security whitepapers, making it an essential resource for researchers. You can easily find various types of exploits, including:
- Remote exploits: Attacking a service over a network without prior access.
- Web Application exploits: Targeting vulnerabilities like SQLi or XSS in web platforms.
- Local and Privilege Escalation exploits: Gaining higher permissions on a system you already have access to.
- Denial of Service (DoS) exploits: Testing the stability and availability of a target.
- Shellcode exploits: Low-level payloads designed to execute specific commands.
Then, if you feel a specific script will work for your target, you can simply copy and paste it into Kali for your attack. Exploits are categorized by platform, type, language, and port in this project to streamline your workflow. To deepen your understanding of this powerful OS, explore our comprehensive guide on What is Kali Linux, where we cover its features, uses, and why it's a go-to choice for cybersecurity professionals globally.
🚀 What is SearchSploit?
SearchSploit is a powerful command-line search tool for Exploit-DB that allows you to take a complete offline copy of the Exploit Database. SearchSploit allows you to perform offline searches through your local repository copy, which is a massive advantage when you are in the field. This capability is especially useful for security assessments on isolated networks or high-security environments without Internet access. By having the database locally, you ensure that your reconnaissance remains stealthy and accessible at all times.
For optimal performance and access to the latest exploit database, make sure your Kali Linux is up to date. Learn more about how to update Kali Linux to keep your system prepared for comprehensive security assessments. If you are running these tests on a remote server, using a Linux VPS can provide the stable environment needed for long-running scans and exploit research.
🛠️ How to install SearchSploit in Kali Linux? [A Guideline to use SearchSploit]
To install SearchSploit, you can use the git clone method to directly clone the repository into your Kali instance. This ensures you have the structure directly from the GitHub repository managed by Offensive Security. Using Git allows for easier manual updates and management of the exploit files.
git clone https://github.com/offensive-security/exploit-database.git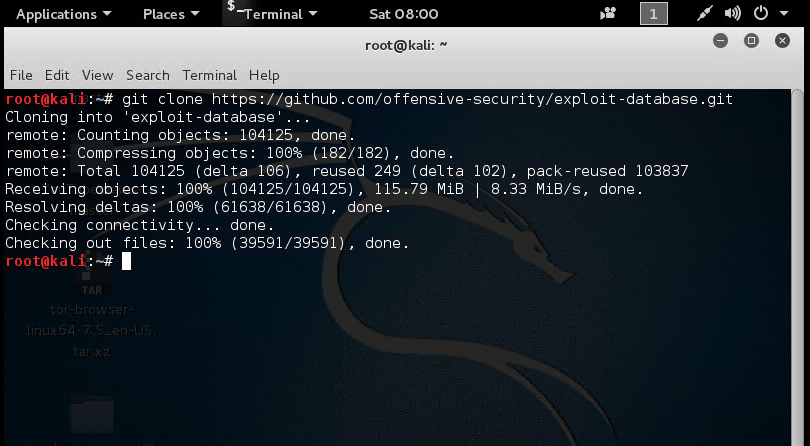
While the git method is great for developers, the most stable way to install it on a standard Kali system is via the package manager. First, refresh your local package index and then install the exploitdb package using the following command:
apt update && apt -y install exploitdb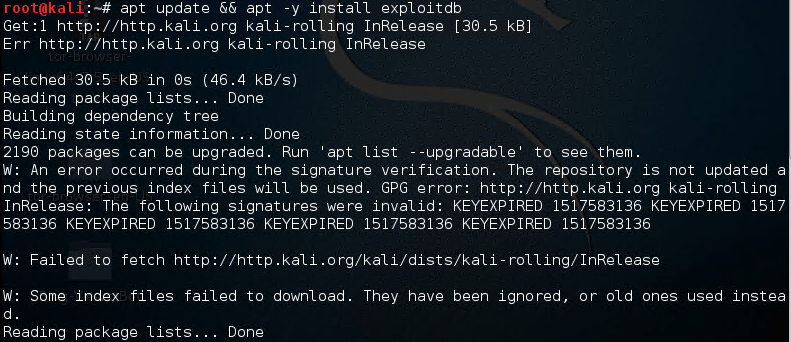
🔍 How to use SearchSploit?
Once installed, the tool is very straightforward to use. By using the " -h " flag, you can see all the features and options that are available to you in the help menu. This is the best way to familiarize yourself with the syntax if you are new to the tool.
root @ kali: ~ # searchsploit -h
Usage: searchsploit [options] term1 [term2] ... [termN]
==========
Examples
==========
searchsploit afd windows local
searchsploit -t oracle windows
searchsploit -p 39446
searchsploit linux kernel 3.2 --exclude = "(PoC) | / dos /"
For more examples, see the manual: https://www.exploit-db.com/searchsploit/
==========
Options
=========
-c, --case [Term] Perform a case-sensitive search (Default is inSEnsITiVe).
-e, --exact [Term] Perform an EXACT match on the exploit title (Default is AND) [Implies "-t"].
-h, --help Show this help screen.
-j, --json [Term] Show result in JSON format.
-m, --mirror [EDB-ID] Mirror (aka copies) an exploit to the current working directory.
-o, --overflow [Term] Exploit titles are allowed to overflow their columns.
-p, --path [EDB-ID] Show the full path to an exploit (and also copy the path to the clipboard if possible).
-t, --title [Term] Search JUST the exploit title (Default is the title AND the file's path).
-u, --update Check for and install any exploitdb package updates (deb or git).
-w, --www [Term] Show URLs to Exploit-DB.com rather than the local path.
-x, --examine [EDB-ID] Examine (aka opens) the exploit using $ PAGER.
--colour Disable color highlighting in search results.
--nmap [file.xml] Checks all results in Nmap's XML output with service version.
Use "-v" (verbose) to try even more combinations
--exclude = "term" Remove values from results. By using "|" You can chain multiple values.
eg --exclude = "term1 | term2 | term3".
=======
Notes
=======
* You can use any number of search terms.
* Search terms are not case-sensitive (by default), and ordering is irrelevant.
* Use '-c' if you want to reduce results by case-sensitive search.
* And / Or '-e' if you want to filter results by using exact match.
* Use '-t' to exclude the file's path to filter the search results.
* Remove false positives (especially when searching using numbers - ie versions).
* When updating or displaying help, search terms will be ignored.
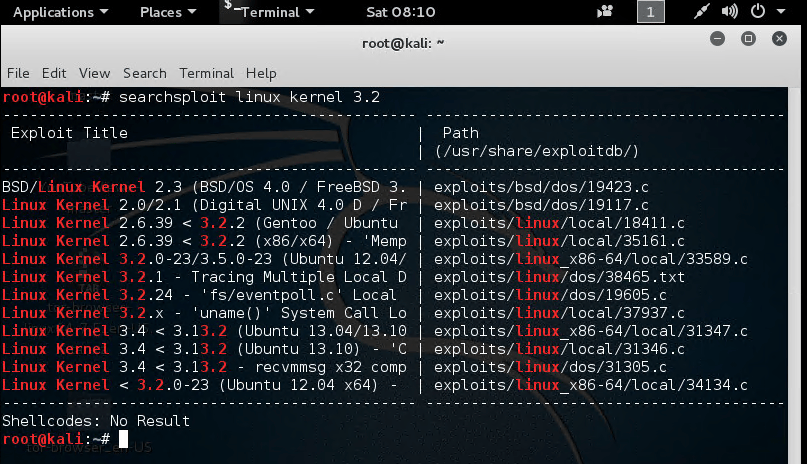
root @ kali: ~ #To demonstrate a practical search, let's look for exploits related to Linux Kernel 3.2. This is a common requirement during privilege escalation phases of a penetration test on older systems. Type this command to search:
searchsploit linux kernel 3.2It will list all the exploits related to Linux Kernel matching those terms, providing the title and the local path to the script.
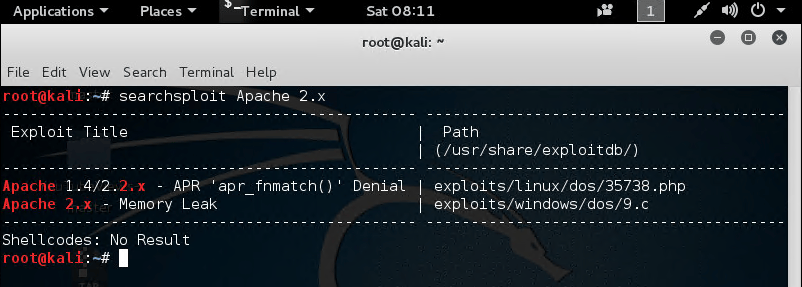
Similarly, you can search for web server vulnerabilities. You can type " searchsploit Apache 2.x " to see these exploits related to Apache 2.x versions. This is incredibly helpful when you identify a service version through reconnaissance tools like Nmap.
🔄 How to Keep SearchSploit Up-to-Date?
The cybersecurity landscape changes daily, with new vulnerabilities (Zero-days) being discovered constantly. To ensure your local database is not obsolete, you must update it regularly. To update SearchSploit, all you need to do is run the following Linux command:
searchsploit -u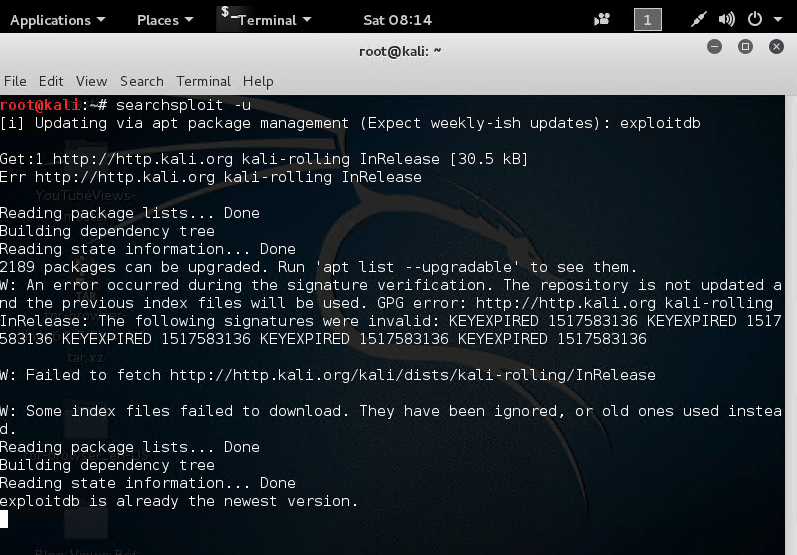
⚠️ Common Mistakes When Using SearchSploit
While SearchSploit is powerful, beginners often run into hurdles. Here are a few things to watch out for:
| Mistake | Consequence | Solution |
| Not updating the database | Missing the latest critical exploits. | Run searchsploit -u weekly. |
| Using too many specific terms | Finding zero results due to strict filtering. | Start broad (e.g., "Apache") and then narrow down. |
| Forgetting the local path | Difficulty in finding the actual file to execute. | Use the -p flag to get the full path to the exploit. |
❓ Frequently Asked Questions
1. Can I use SearchSploit on other Linux distributions?
Yes! While it comes pre-installed on Kali, you can install it on Ubuntu, Debian, or even CentOS by cloning the repository from GitHub as shown in our installation guide.
2. Does SearchSploit run the exploits automatically?
No. SearchSploit is a search tool, not an execution framework. It helps you find the code; you must then inspect the code and run it manually or via a compiler.
3. Why do some exploits have "PoC" in the title?
"PoC" stands for Proof of Concept. These scripts are meant to prove a vulnerability exists but might not provide a full "root" shell without modification.
🏁 Conclusions
Congratulations! You have learned how to install SearchSploit on Kali Linux VPS and how to use it to find vulnerabilities. For those serious about penetration testing, having a dedicated environment is key. Feel free to comment here if you encounter any problems during the installation; we will help you to solve the issue. You can also buy Linux VPS to practice your skills on a routine basis in a secure, isolated environment.
If you're looking to further enhance your Kali Linux setup, consider checking out our guide on installing OpenVAS in Kali Linux for advanced vulnerability scanning and network security analysis.
People Are Also Reading:

Leave A Comment